Threat Intelligence and Threat Hunting, 2nd Edition
ISBN: 0135342104 | .MP4, AVC, 1280x720, 30 fps | English, AAC, 2 Ch | 4h 58m | 1.15 GB
Instructor: Aamir Lakhani
ISBN: 0135342104 | .MP4, AVC, 1280x720, 30 fps | English, AAC, 2 Ch | 4h 58m | 1.15 GB
Instructor: Aamir Lakhani
Video description
Explore key threat intelligence and threat hunting concepts to help you protect your sensitive data.
A cybersecurity professional needs to understand threats, threat actors, and have a clear understanding of where attackers are trying to take advantage of vulnerabilities. The Threat Intelligence and Threat Hunting, 2nd Edition video course provides learners with the knowledge and skills to fortify systems, protect sensitive data, and ensure compliance with privacy regulations.
Throughout the course, expert trainer, author, and cybersecurity expert Aamir Lakhani uses hands-on demos, in-depth discussions and lightboard explanations to explore how to classify threats, work with the vulnerabilities, and use common assessment methodologies. By the end of this course, you will be able to protect sensitive data and ensure compliance with privacy regulations, secure systems and applications to prevent data exposure and advise your organization on privacy-by-design principles.
Topics include:
- Threat-Intelligence and Threat-Hunting Concepts
- Analyze Indicators of Potentially Malicious Activity
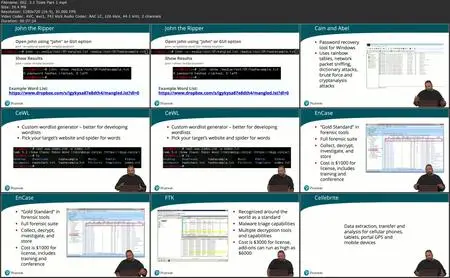
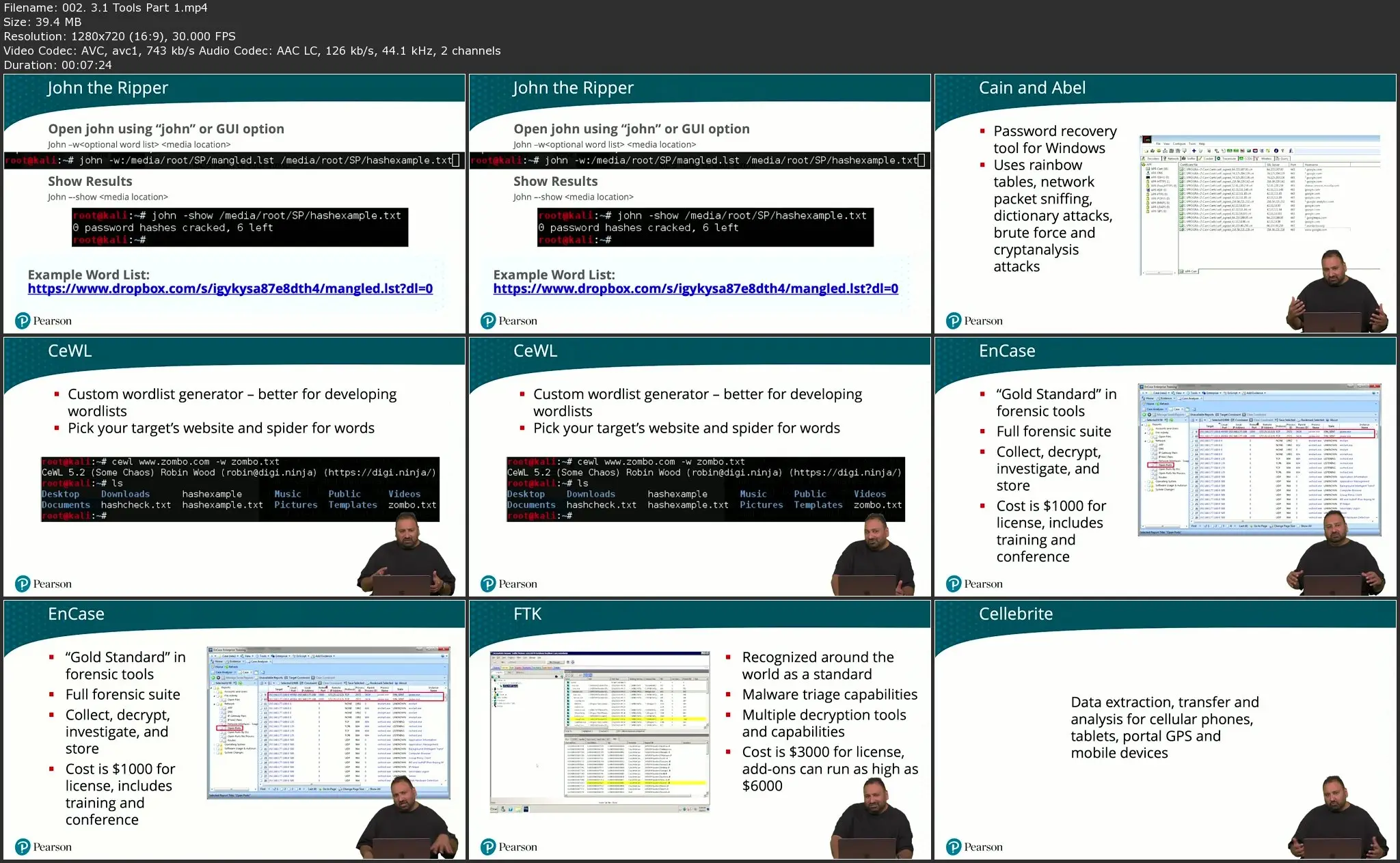
- Tools or Techniques to Determine Malicious Activity
- Concepts Related to Attack Methodology Frameworks
- Utilizing Threat Intelligence to Support Organization Security
- Analyze Output from Common Vulnerability Assessment Tools
- Threats and Vulnerabilities Associated with Specialized Technology
Skill Level:
Beginner
Learn How To:
- Apply key threat intelligence and threat hunting concepts
- Understand and classify hot attacks are taking advantage of vulnerabilities
- Use common vulnerability assessment methodologies
- Understand threats against Internet of Things, real-operating systems, and cloud-based environments
Who Should Take This Course:
- Cybersecurity Professionals
- Anyone interested in learning cyber security fundamentals.