File Upload Flaws Mastery: Hands-on from Zero to Hero!
.MP4, AVC, 1280x720, 30 fps | English, AAC, 2 Ch | 1h 6m | 561 MB
Instructor: Martin Voelk
.MP4, AVC, 1280x720, 30 fps | English, AAC, 2 Ch | 1h 6m | 561 MB
Instructor: Martin Voelk
Become professional in finding and exploiting File Upload Vulnerabilities. For Ethical Hackers and Bug Hunters
What you'll learn
- file upload vulnerabilities
- remote code execution (RCE)
- bypassing file upload filters
- penetration testing
- bug bounty hunting
- Walkthrough of all File Upload Vulnerabilities Apprentice and Practitioner Labs from Portswigger
- Extra File Upload vulnerability lab
Requirements
- Basic IT Skills
- Basic understanding of web technology
- No Linux, programming or hacking knowledge required
- Computer with a minimum of 4GB ram/memory
- Operating System: Windows / Apple Mac OS / Linux
- Reliable internet connection
- Burp Suite Community (Pro optional)
- Firefox Web Browser
Description
Welcome to the File Upload Vulnerabilities Mastery Class – From Zero to Hero!
This class combines both theory and practical hands-on lab experience to find and exploit File Upload Vulnerabilities vulnerabilities in modern applications (web apps, APIs and mobile).
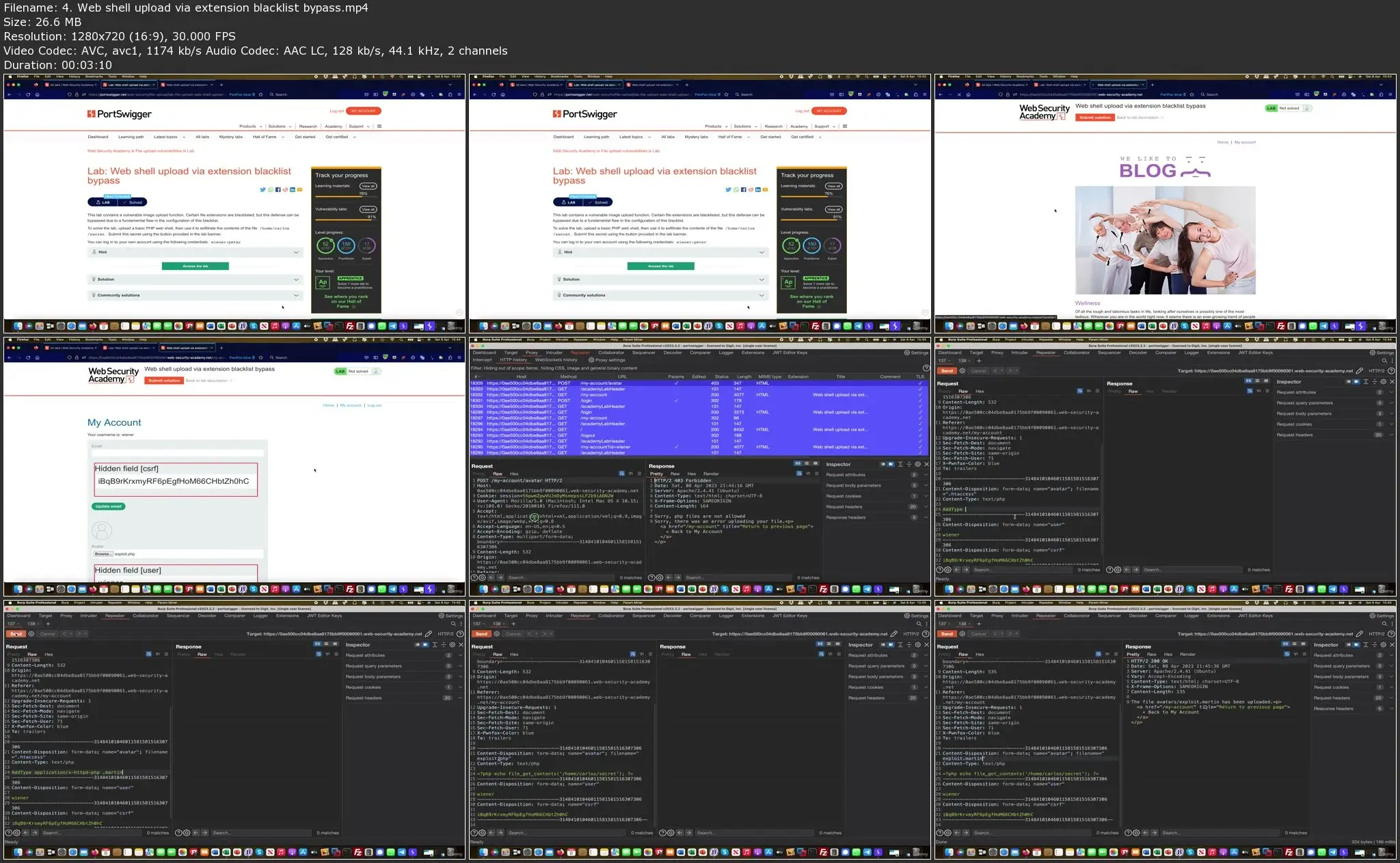
Important note: This course is NOT teaching the actual usage of Burp Suite and its features. This course is proving a step-by-step walkthrough through the practitioner labs with detailed explanations on how to find and exploit web app vulnerabilities.
Your instructor is Martin Voelk. He is a Cyber Security veteran with 27 years of experience. Martin holds some of the highest certification incl. CISSP, OSCP, OSWP, Portswigger BSCP, CCIE, PCI ISA and PCIP. He works as a consultant for a big tech company and engages in Bug Bounty programs where he found thousands of critical and high vulnerabilities over the years.
This course features all current apprentice and practitioner PortSwigger Web Security Academy lab walk-throughs in the File Upload Vulnerabilities section. In addition, it features a full theory portion which explains the different types of File Upload Vulnerabilities.
Martin is solving all these labs and giving useful insight on how to find and exploit these vulnerabilities. He is not just inserting the payload but explains each step on finding the vulnerability and why it can be exploited in a certain way. The videos are easy to follow along and replicate. Martin is also dropping a lot of tips and tricks for real-world Penetration Testing or Bug Bounty Hunting.
This training is highly recommended for anyone who wants to become a professional in Web Application Penetration Testing, Web Application Bug Bounty Hunting and wants to focus at 1 vulnerability class at a time.
It will feature all Apprentice and Practitioner Labs in the File Upload Vulnerabilities section.
The theory portion discusses the concepts around:
· File Extension bypass
· Content-Type bypass
· Path traversal bypass
· .htaccess bypass
· extension bypass
· Image upload and bypasses
· Webshells
· Polyglots
· Examples
· Finding File Upload Vulnerabilities Vulnerabilities
The lab portion will feature:
· Walkthrough of all File Upload Vulnerabilities Apprentice and Practitioner Labs from Portswigger
· Additional Lab on File Upload Vulnerabilities
Notes & Disclaimer
Portswigger labs are a public and a free service from Portswigger for anyone to use to sharpen their skills. All you need is to sign up for a free account. I will update this course with new labs as they are published. I will to respond to questions in a reasonable time frame. Learning Web Application Pen Testing / Bug Bounty Hunting is a lengthy process, so please don’t feel frustrated if you don’t find a bug right away. Try to use Google, read Hacker One reports and research each feature in-depth. This course is for educational purposes only. This information is not to be used for malicious exploitation and must only be used on targets you have permission to attack.
Who this course is for:
- Anybody interested in ethical web application hacking / web application penetration testing
- Anybody interested in becoming a web application bug bounty hunter
- Anybody interested in learning how hackers hack web applications
- Developers looking to expand on their knowledge of vulnerabilities that may impact them
- Anyone interested in application security
- Anyone interested in Red teaming
- Anyone interested in offensive security